- Best for workforce and customer identity: OpenIAM
- Best for fine-grained authorization: Keycloak
- Best for seamless integration and cross-platform compatibility: Ory
- Best for versatility: Aerobase Server
- Best AI-driven open-source IAM: ForgeRock (Ping Identity)
- Best for higher education or research institutions: Shibboleth Consortium
Identity access management (IAM) tools, crucial for cybersecurity, have become highly sought-after due to rising identity-related breaches. A Statista report revealed that 80% of global respondents experienced cyber breaches linked to authentication vulnerabilities in 2023. Additionally, 70% of US-based IAM professionals expressed concerns about identity-based threats.
IAM tools help organizations secure and manage user identities and access to resources, ensuring only authorized individuals gain access. While proprietary IAM solutions like Okta, OneLogin and Cyberark dominate the market, open-source IAMs offer flexibility and low cost. Let’s explore their features, pricing, benefits and limitations.
Best open source IAM tools comparison
The following table provides a snapshot of how these open-source IAMs compare to each other.
| Identity lifecycle management | Multi-factor Authentication (MFA) | Single Sign-on (SSO) and Single Logout (SLO) | Pricing | |
|---|---|---|---|---|
| OpenIAM | Yes | Adaptive MFA | Yes | Free version or subscription; contact vendor for a quote. |
| Keycloak | Yes | Yes | Yes | Free. |
| Ory | Yes | Yes | Yes, within certain subscriptions. | Free version for EU region; US and EU plans starting at $29/month. |
| Aerobase Server | Yes | Yes | Yes, for browser applications. | Free version or plans starting at $690/month. |
| ForgeRock | Yes | Yes | Yes, when configured. | Starts at $3 per user per month for Workforce plans. |
| Shibboleth Consortium | Yes | MFA profile standard for IdPs. | Only supported on Shibboleth 3.2 and above. | Starts at $2,960/year. |

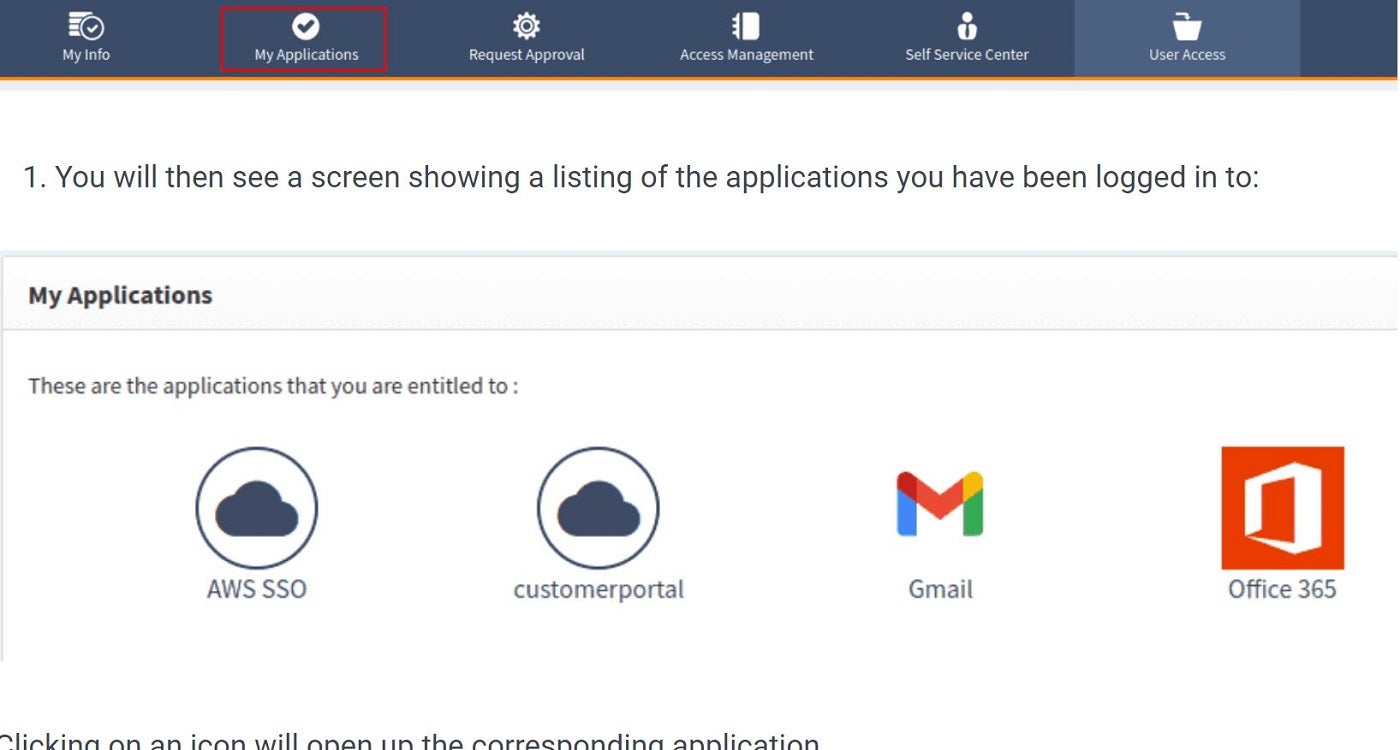
This open-source IAM solution caters to both workforce and customer identities. Suitable for enterprise use, it offers organizations a set of features designed to streamline user access across various platforms. It boasts a robust web access control for identity management, diverse applications, Single Sign-On (SSO), Desktop SSO and API integration controls. It also includes Two-Factor/Multi-Factor Authentication (2FA/MFA) and role-based access control management. In addition to these core features, OpenIAM provides supplementary capabilities like SSH key management, session management and password vault, as well as several deployment options for both cloud and on-premises deployments.
Why we chose OpenIAM
We selected OpenIAM for its extensive enterprise-level features that can manage both internal and external users from a single IAM platform.
Pricing
OpenIAM is available in two versions: Community Edition (CE) and Enterprise Edition (EE). The CE is a free version of OpenIAM that customers can deploy in their environments. The CE operates as a previous generation of the Enterprise Edition. For example, when v4.2.1 of the Enterprise was released, 4.2.0.x was made available to the public as the CE. Therefore, the CE will always have fewer features than the EE.
Features
- Single sign-on using SAML 2, oAuth 2 and OpenID Connect (OIDC).
- Role-based access control.
- API integration controls.
- 2FA and MFA security.
- Automated user onboarding and offboarding.
Pros
- Free version.
- Built on a modern architecture that supports RPM, Kubernetes and OpenShift deployments.
- Simplifies compliance activities.
- Automates identity life cycle events.
- Detects and remediates SoD violations.
- Provides seamless integration across platforms.
Cons
- Consent management is not available on the community edition.
- There is no pricing information.

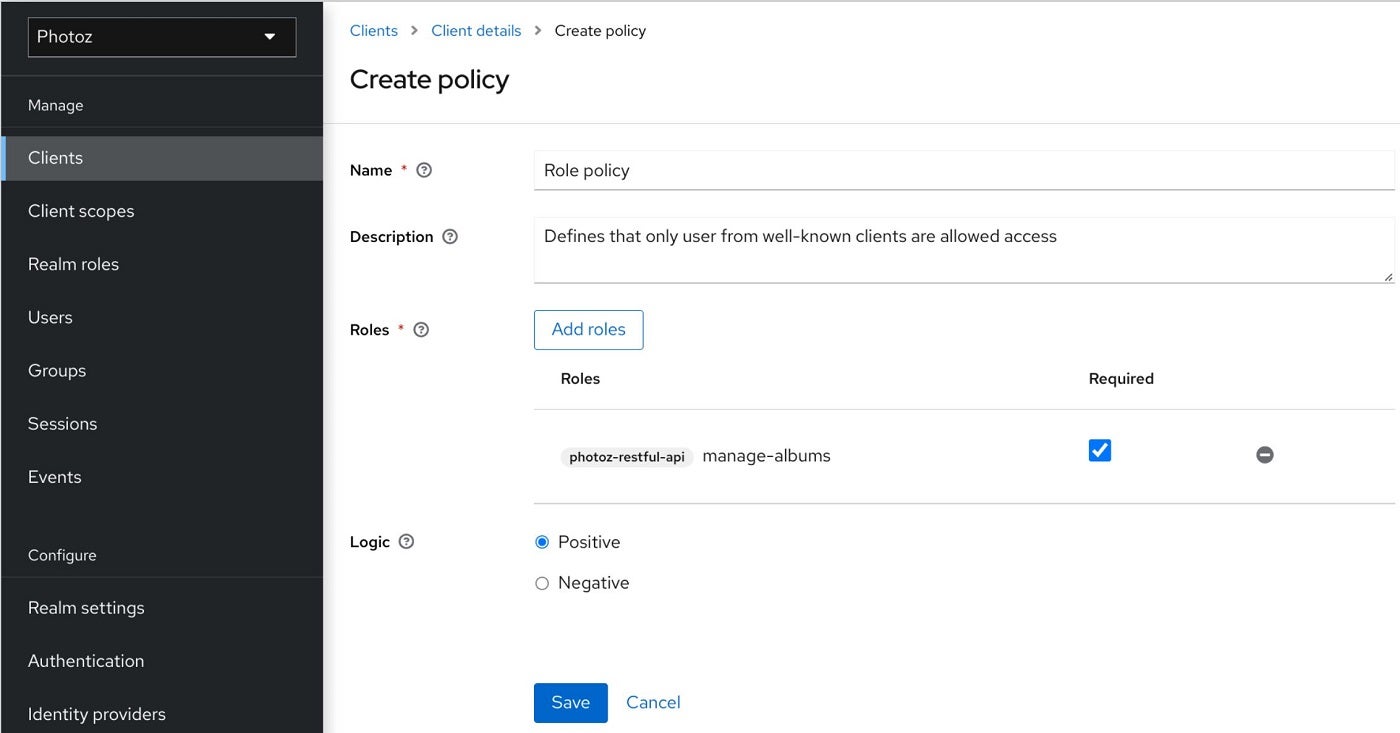
Keycloak’s IAM platform offers identity brokering and social login that enable users to authenticate with existing OpenID Connect or SAML 2.0 Identity Providers and social networks. Its user federation feature allows connection to existing LDAP or Active Directory servers. Administrators can manage all aspects of the Keycloak server through its admin console. Keycloak adheres to standard protocols such as OpenID Connect, OAuth 2.0 and SAML and provides fine-grained authorization services that support different access control mechanisms like attribute-based access control (ABAC), role-based access control (RBAC), user-based access control (UBAC), rule-based access control and context-based access control (CBAC).
Why we chose Keycloak
We chose Keycloak for its fine-grained authorization services, which provide precise control over access and permissions.
Pricing
This solution is free and open to all.
Features
- Identity Brokering and Social Login.
- User federation.
- Centralized management.
- Fine-grained authorization.
- Built on standard protocols.
Pros
- Free.
- Offers single sign-on and single sign-outs for multiple applications.
- Supports LDAP and active directory connection.
- Seamless user authentication with existing identity providers.
- Provides comprehensive documentation for configuration, implementation and optimization.
- Offers customizable functionality and extensibility for business integrations.
Cons
- Initial setup can be complex for novice users.

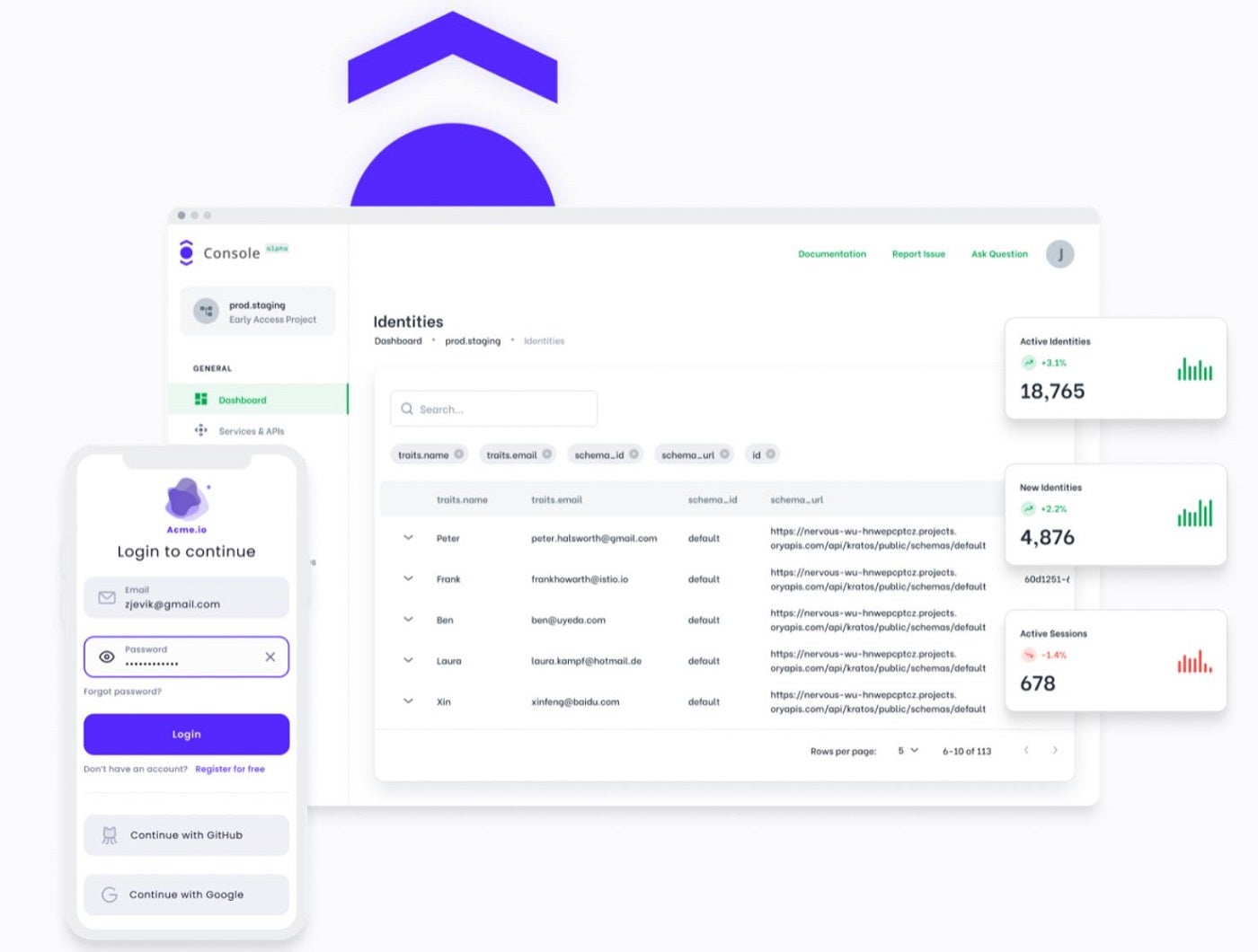
Ory offers an open-source infrastructure solution for building a zero-trust network. Its suite of open-source projects, including Ory Kratos Identity Server, Ory Hydra Federation Server and Ory Keto Permission Server, provides robust identity management, access control and authentication via standards like OAuth 2.0/2.1 and OpenID Connect. Ory’s services and APIs are developed and licensed under Apache 2.0, allowing users to contribute and understand the solution. The platform’s flexibility allows users to customize authentication and authorization experiences, while its commercial offering, Ory Network, provides scalability.
Why we chose ORY
We selected ORY because of its customizable UI, flexible deployment options and extensive API, all of which add versatility to the tool.
Pricing
Ory is available in four plans:
- Developer: Free for EU region.
- Essentials: $29/month and $319/year.
- Scale: $690/month and $7,590/year.
- Enterprise: Covers everything from the first two packages, plus additional features and dedicated support. For a custom quote, contact the vendor.
Features
- MITREid compatibility.
- Cryptographic Key Storage.
- Robust API and intuitive CLI.
- Flexible deployment.
- OAuth2 and OpenID Connect protocol.
Pros
- Ensures compatibility with modern structures with its cloud-native architecture.
- Offers flexible deployment options.
- Supports industry-standard protocols.
- Offers swift onboarding with the Ory Network.
- Runs on an easily scalable platform.
Cons
- While it offers flexibility, customization options may be complex for novices.
- SSO not offered in Developer and Essentials plans.

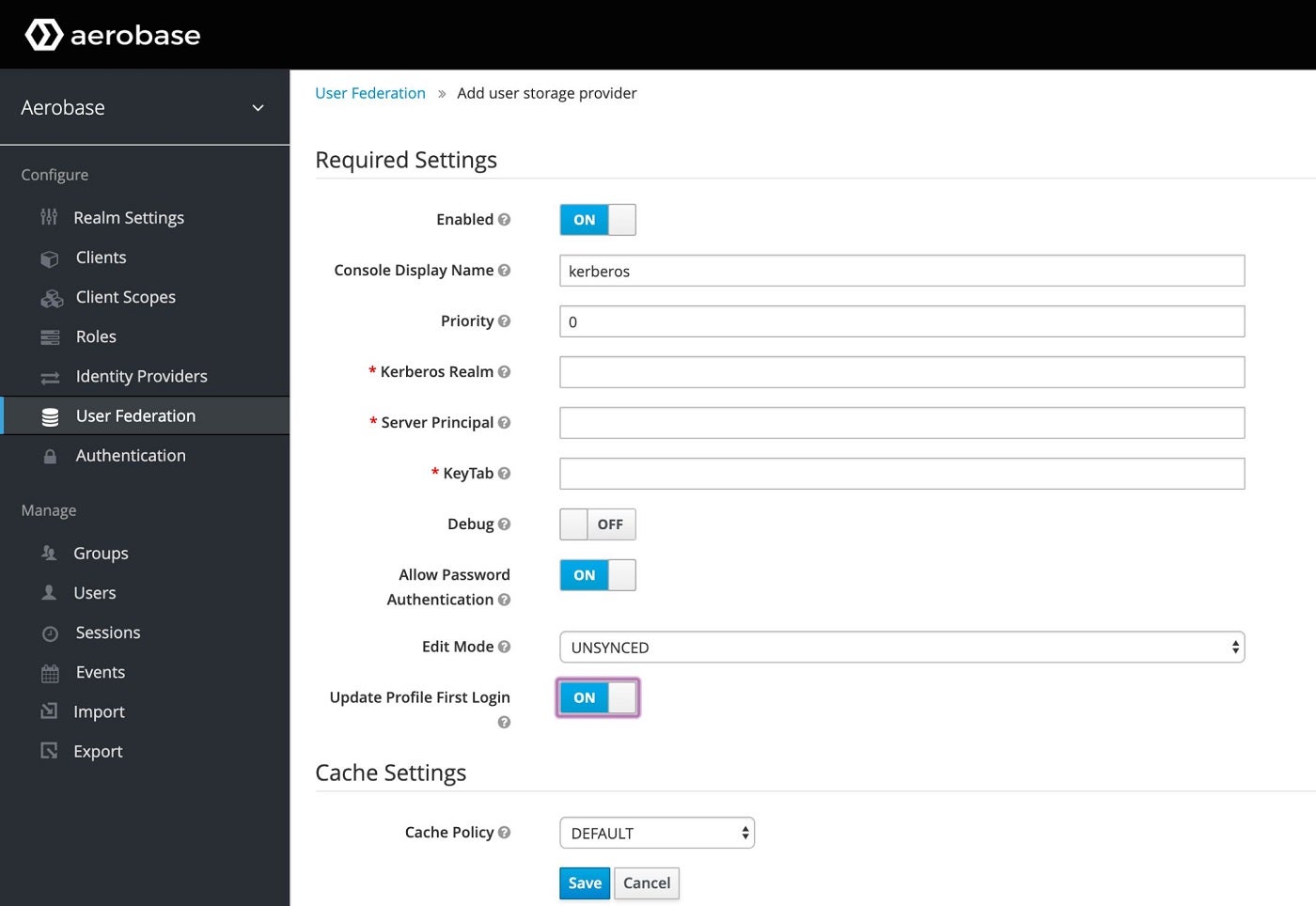
Aerobase Server is an IAM solution tailored for cloud, on-premises and hybrid deployments. It encompasses features such as identity federation, Single Sign-On (SSO), adaptive authentication, account management and identity provisioning. In addition to offering microservices security, it runs on the OpenID Connect, CAS and SAML 2 protocols and integrates with third-party authentication, social identity providers, diverse applications, systems and databases. This tool also allows users to customize IAM policies, workflows and interfaces.
Why we chose Aerobase Server
We chose this tool for its ability to adapt seamlessly to diverse deployment scenarios—cloud, on-premises and hybrid—as well as provide IAM solutions across varied environments.
Pricing
Aerobase’s Open Source version is free. It also offers subscriptions: Basic, Enterprise and OEM.
- Basic: $690/month (billed annually).
- Enterprise: $2,250/month (billed annually).
- OEM: Contact vendor for a quote.
Features
- OpenID Connect, SAML and CAS.
- Fine-grained authorization.
- Identity federation.
- Multi-factor authentication.
- Cloud, on-premises and hybrid deployment.
Pros
- Offers long-term customer support for paid plans and community support for all plans.
- Provides user lifecycle management.
- Ensures audits and privacy compliance.
- Demonstrates strong integration capabilities across diverse environments.
- Allows customization to suit the organization’s specific needs.
Cons
- The free version is limited and does not have a cloud test instance.

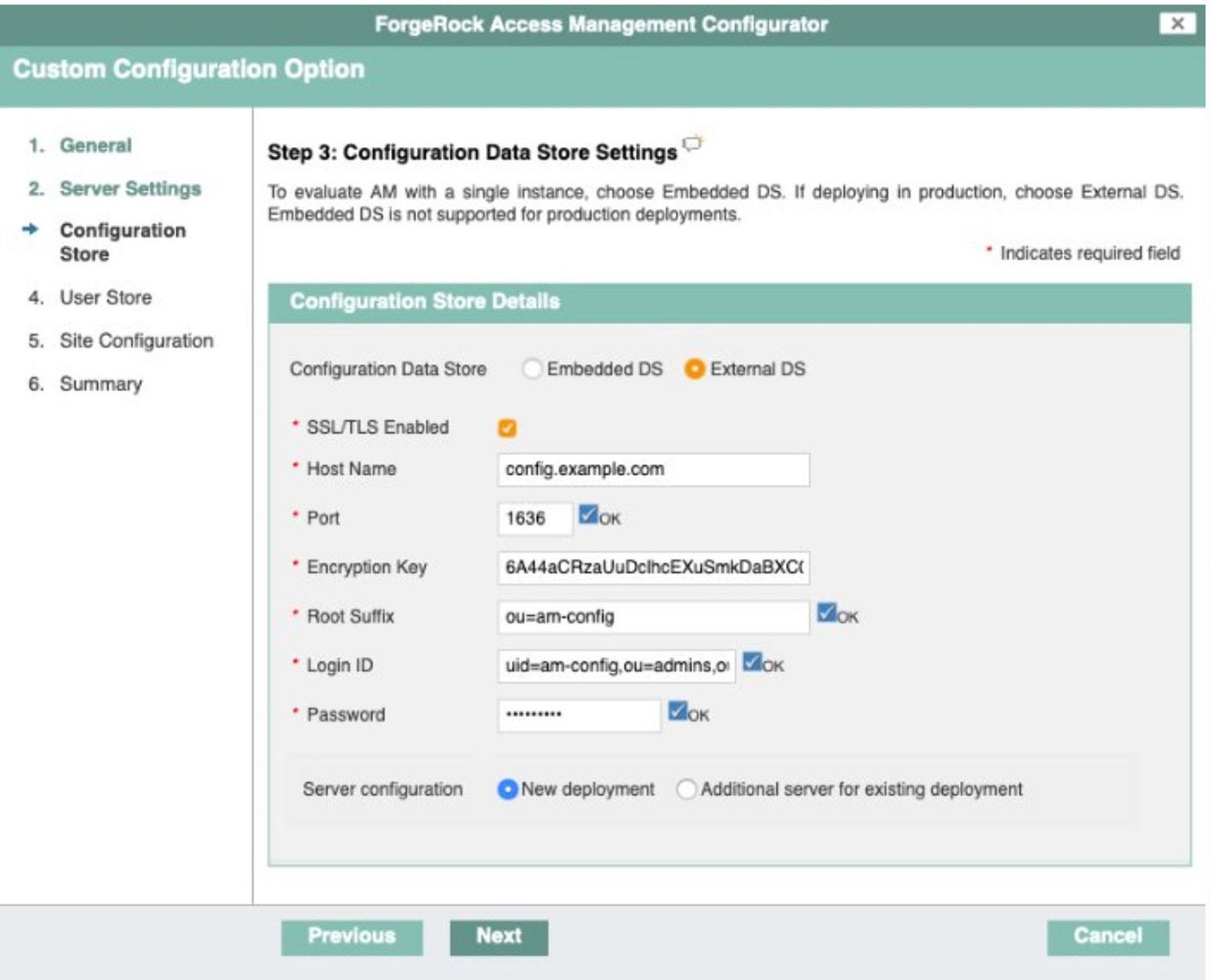
ForgeRock, now merged with Ping Identity, provides a modern, modular and cloud-ready platform architecture that is suitable for multi-cloud and hybrid environments. It offers advanced features in Customer and Workforce Identity Management, including fraud and risk protection, identity verification, decentralized identity, fine-grained authorization, lifecycle management and identity governance and administration (IGA). This solution utilizes AI and Machine Learning to inspect and adapt real-time access based on behavior/user activity, accounts and roles to automatically approve, provision or certify access, ensuring end-to-end management.
Why we chose ForgeRock (Ping Identity)
ForgeRock was picked for its AI-driven IAM and emphasis on fraud and risk protection for organizations.
Pricing
ForgeRock (Ping Identity) offers two tiers: PingOne for Customers and PingOne for Workforce. Each tier has three plan options.
- PingOne for Customers
- Essential: Starting at $20K per year.
- Plus: Starting at $40K per year.
- Premium: Contact sales for pricing.
- PingOne for Workforce
- Essential: Starting at $3 per user per month, for a minimum of 5,000 users.
- Plus: Starting at $6 per user per month, for a minimum of 5,000 users.
- Premium: Contact sales for pricing.
Features
- Unified cloud administration
- Intelligent access for registration, authentication and management.
- Enterprise-grade security.
- Identity governance and administration (IGA).
- Identity lifecycle management.
Pros
- Offers customer and workforce identity management.
- Enhances identity management and governance.
- Provides a unified cloud administration.
- Provides out-of-the-box connectors, APIs and SDKs for easy integration.
- Compliance with data privacy regulations.
Cons
- Pricing not designed for small businesses.
- May be costly for individuals.
Shibboleth Consortium: Best for higher education or research institutions

Shibboleth, developed and overseen by the Shibboleth Consortium, offers web-based single sign-on (SSO) and federated identity solutions, mainly for higher education and research institutions. This tool provides organizations the capability to expand their user authentication systems, granting access to online resources from associated organizations and promoting seamless inter-organizational collaboration. It also offers centralized auditing and reporting capabilities for user authentication events and application access and supports federated authentication and user attribute exchange.
Why we chose Shibboleth Consortium
Shibboleth was chosen for its standout resource-sharing capabilities and user authentication, and application access features that facilitate authentication management across organizations.
Pricing
Shibboleth Consortium offers five membership tiers. Three of the tiers have plans for small, medium and large organizations.
- NREN/Federation Members: This category has three tiers and they are billed based on the total number of Identity Providers (IdPs) and Service Providers (SPs) in their constituencies.
- Small: €12,500 / $14,800 (up to 250 IdPs & SPs).
- Medium: €25,000 / $29,600 (251-750 IdPs & SPs).
- Large: €50,000 / $59,200 (750+ IdPs & SPs).
- Academic/Non-Profit Organizations: This category has three tiers and they are billed based on the total number of users.
- Small: €2,500 / $2,960 (up to 10,000 users).
- Medium: €5,000 / $5,920 (10,000-50,000 users).
- Large: €7,500 / $8,880 (50,000+ users).
Note: These rates are for 2024 and will increase by 10% in 2025.
- Commercial Organizations: Charged based on revenue.
- Small: €5,000 / $5,920 (up to €10m)
- Medium: €10,000 / $11,840 (€10m-€100m)
- Large: €20,000 / $23,680 (€100m+)
The Multi-site Academic category and Principal Membership tiers are based on individual/organizational preference and they are billed at $29,600 and $25,000, respectively.
Features
- Embedded discovery service.
- Federated identity management.
- Open-source collaborations.
- Centralized auditing and reporting.
- User attributes exchange.
- Single Sign-On.
Pros
- Adheres to interoperability standards.
- Offers community support.
- Provides access to expertise.
- Offers collaborative resources via attributes exchange/resource sharing.
- Considers users needs and influence in software development for better alignment.
- Multiple plan options.
Cons
- Official technical support is unavailable to unpaid users.
Key features of open-source IAM tools
Open-source IAM tools offer a range of features that cater to the needs of organizations looking for efficient identity and access management solutions without the constraints of proprietary software. Below are some key features of these tools.
Identity management
This encompasses managing user identities throughout their lifecycle, including user provisioning, updating user access, de-provisioning, account management and profile synchronization across various systems and applications. Most open-source IAM tools offer centralized identity storage and directories to store and manage user attributes, credentials and entitlements, ensuring consistency and accuracy of identity data across the organization. This enables organizations to efficiently onboard new users, update user information, enforce password policies, revoke or restore access and deactivate or delete user accounts when necessary.
User Authentication and Authorization
Open-source IAM tools create mechanisms to verify the identity of users accessing resources within the system. This involves validating credentials, such as usernames and passwords, against a user database or directory. Once a user’s identity is confirmed, the tool implements access controls to determine what resources the user is permitted to access and what actions they can perform. These authorization policies are defined by user roles, permissions, attributes and contextual information.
Single Sign-On (SSO)
This feature allows users to log in once and gain access to multiple applications and services without having to re-enter their credentials separately for each one. Open-source tools use diverse protocols such as SAML, OAuth, CAS and OpenID Connect to enable seamless authentication and access to resources with a single login across different systems and domains.
Multi-Factor Authentication (MFA)
MFA enhances security by requiring users to provide multiple forms of verification before accessing sensitive resources. This involves a combination of factors such as passwords, OTPs, biometrics, security questions and sometimes passkeys. Open-source IAM solutions integrate MFA capabilities to strengthen authentication processes and mitigate the risk of unauthorized access, especially in environments where security is a top priority.
Audit and Compliance
Open-source IAM Solutions offer auditing and reporting functionalities to track user activities, access attempts and administrative changes within the system. The audit logs capture relevant information such as user login/logout events, access to sensitive resources, policy changes and security incidents, helping organizations maintain visibility into their IAM environment and ensuring compliance with regulatory requirements (e.g., GDPR, HIPAA, PCI-DSS).
How do I choose the best open-source IAM tool for my business?
When choosing an open-source AIM tool for your business, consider the size of your organization, the industry you’re in and the complexity of your IT infrastructure. Evaluating the features of the IAM tool is another important step. Look for capabilities such as user provisioning, authentication, authorization and audit capabilities. The tool’s scalability and flexibility are also key, as they ensure the tool can grow with your business and adapt to changing needs. Community support and the frequency of updates are other important factors you need to check in an open-source tool, as they can indicate the tool’s reliability and longevity.
Methodology
My review process involved a comprehensive analysis of the current market for open-source IAM tools, after which I selected these six based on factors such as popularity, community support and the robustness of features. While no hands-on testing was conducted due to a lack of a testing environment, a significant amount of research was undertaken to understand each tool’s capabilities and performance. This included watching demo videos and consulting each vendor’s site and external resources such as user reviews and industry reports to gain a broader perspective.


